External FedRAMP Assessment
Conquer the Contextual Certainty Deficit: Automate FedRAMP 20x Persistent Validation and Eradicate the Hidden Tax on Your SOC
The End of Compliance Theater. The transition to FedRAMP 20x is fundamentally changing how cloud service providers operate, permanently replacing static compliance documents with continuous, machine-readable, persistent validation. For CISOs, 3PAO Practice Directors, and MSSP SOC Managers, relying on legacy scanners that dump uncontextualized vulnerabilities onto your team creates a massive "Contextual Certainty Deficit". This forces your highly compensated analysts into a reactive state, manually hunting down algorithmic false positives, a "Hidden Tax on the SOC" that drains enterprise resources and stalls engineering velocity. ThreatNG's External FedRAMP Assessment provides a definitive, unauthenticated attacker's perspective of your boundary, discovering the "Ghost Assets" your internal tools miss. By automatically mapping external findings directly to NIST 800-53 controls and FedRAMP Key Security Indicators (KSIs), ThreatNG empowers you to definitively defend your perimeter, secure your Authority to Operate (ATO), and turn compliance into a strategic revenue engine.
From Algorithmic Guesswork to Mathematical Proof:
Conquer the FedRAMP 20x Mandate, Secure Your Perimeter, and Reclaim Your Security Operations

Eradicate the "Hidden Tax on the SOC" with Legal-Grade Attribution
Stop paying the operational penalty of chasing ghost assets and algorithmic false positives generated by context-blind tools. ThreatNG operates frictionlessly from the outside in, using unauthenticated Recursive Discovery to find the shadow IT, forgotten SaaS applications, and orphaned subdomains that traditional internal scanners overlook. Our Context Engine™ then mathematically verifies asset ownership, providing the irrefutable "Legal-Grade Attribution" required to eliminate alert fatigue. This allows your elite security personnel to stop acting as administrative clerks and return to proactively defending the business.
Achieve "Contextual Certainty" for NIST SC-7 Boundary Validation
In the fight against sophisticated adversaries and bureaucratic audit friction, traditional document reviews are dead. ThreatNG provides a definitive advantage by continuously assessing your external perimeter, exactly as an advanced attacker would. We translate raw technical findings—such as exposed RDP ports or missing Web Application Firewalls—into direct, deterministic failures of NIST SC-7 Boundary Protection controls. This grants you and your 3PAO auditors undeniable, mathematical proof of your security posture, ensuring your authorization boundary matches reality before the formal assessment even begins.

Automate Persistent Validation for the FedRAMP 20x Mandate
With the FedRAMP 20x machine-readable mandate approaching, manual document gathering is no longer just an expensive operational burden; it is a direct threat to your federal contract pipeline. ThreatNG serves as your automated compliance translation engine, converting continuous external reconnaissance data directly into the structured Key Security Indicators (KSIs) demanded by the new federal framework. Through dynamic Correlation Evidence Questionnaires (CEQs), we instantly generate questionnaires backed by the evidence collected by ThreatNG, requiring policy validation and enabling you to effortlessly produce continuous, state-based authorization data.
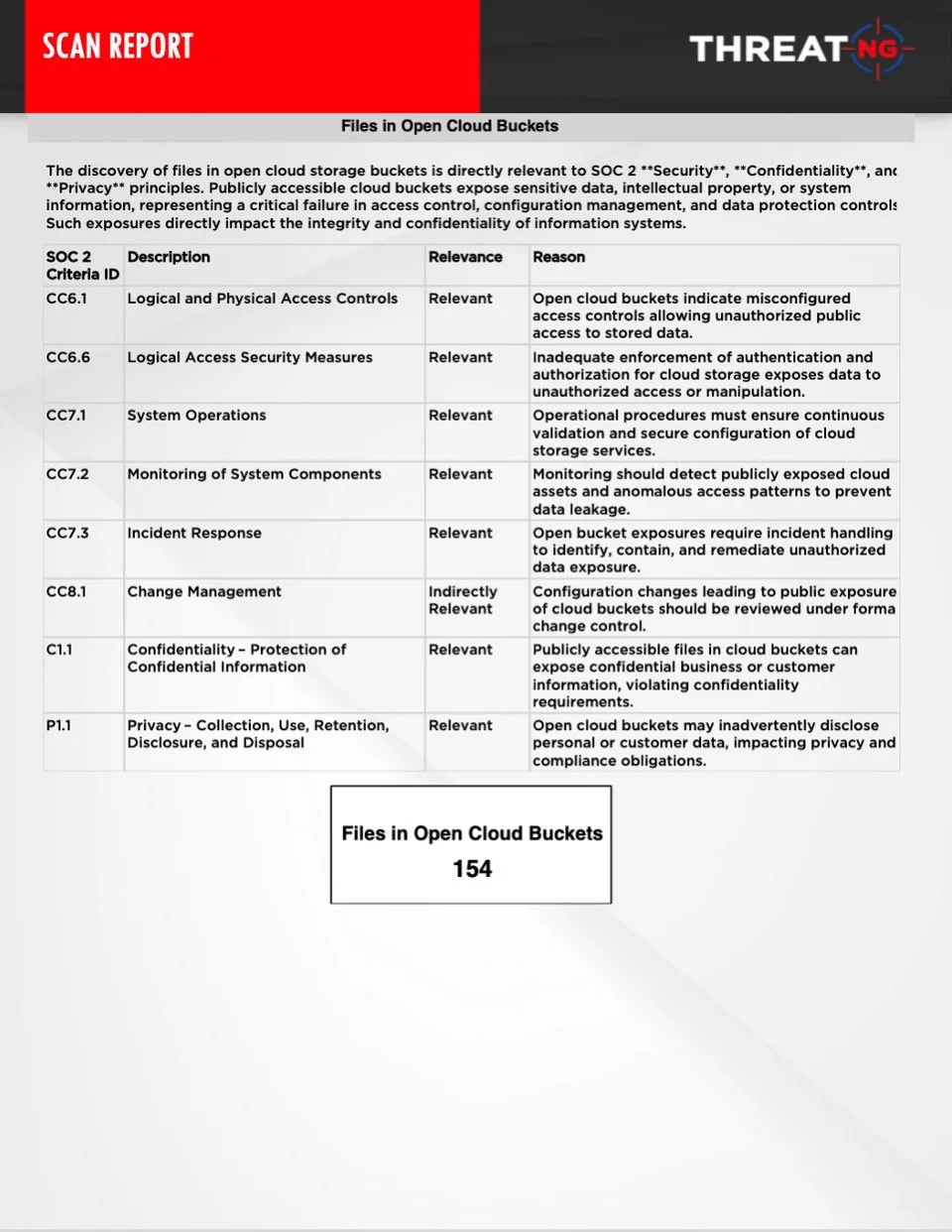
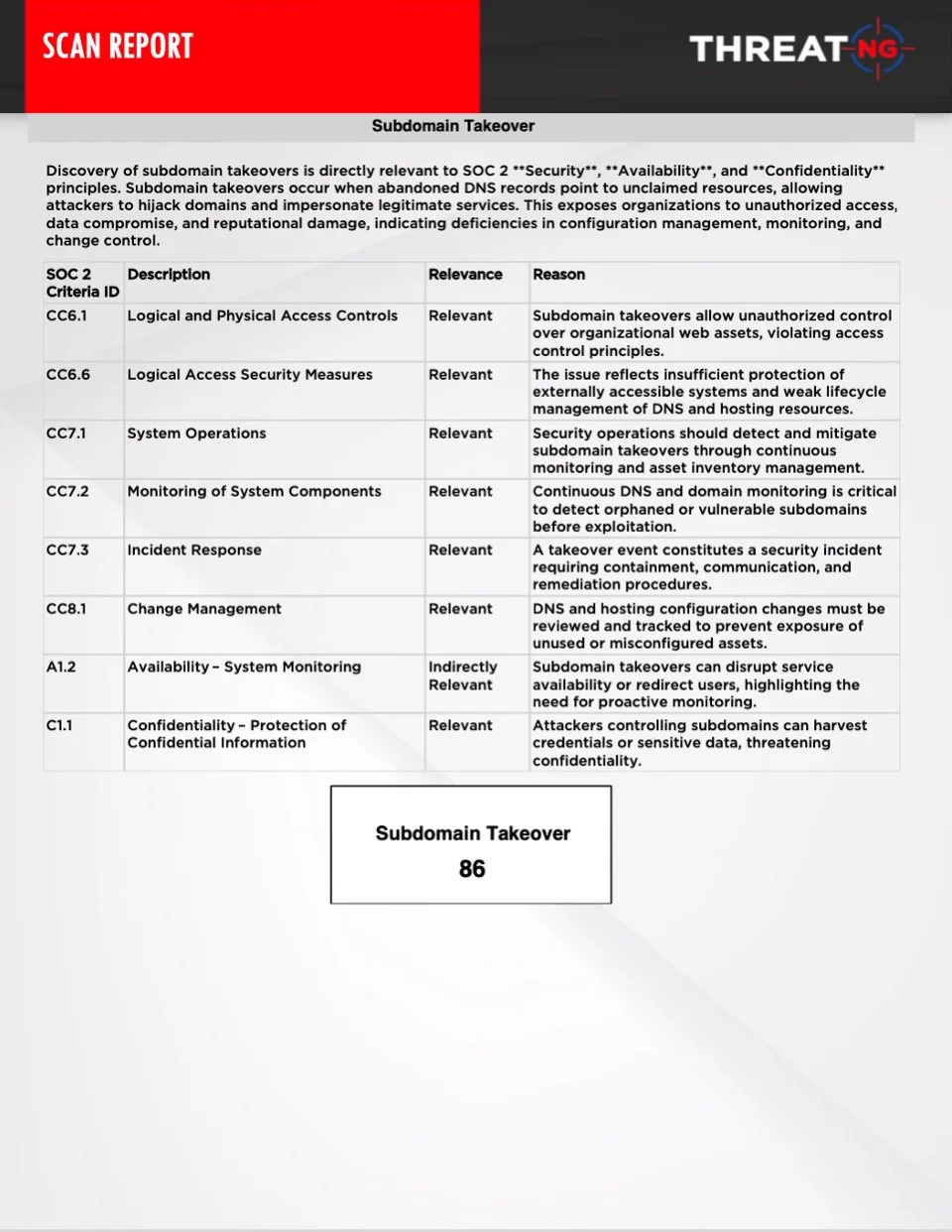
Automated GRC Reporting: Translating External Exposures into FedRAMP Compliance Evidence
ThreatNG’s External GRC Assessment reporting capability automatically translates unauthenticated external findings into customizable, prioritized reports that map directly to specific FedRAMP and NIST 800-53 control IDs. For example, the discovery of a missing Web Application Firewall (WAF) or a vulnerable public-facing login page is explicitly documented in the report as a definitive failure of the NIST SC-7 (Boundary Protection) control. Similarly, if the platform detects subdomains missing a Content Security Policy (CSP), the generated evidence maps this directly to deficiencies in configuration settings (CM-6) and continuous monitoring (CA-7). By converting raw technical flaws into clear, auditable compliance documentation, ThreatNG delivers the mathematically verifiable proof required for security leaders to demonstrate proactive risk management (RA-3, RA-5), successfully navigate rigorous federal audits, and protect the organization from the severe revenue losses associated with delayed or revoked authorizations.
Why ThreatNG?
For End Organizations (Cloud Service Providers)
Replace the anxiety of subjective, point-in-time audits with the absolute certainty of continuous, machine-driven validation. ThreatNG’s External FedRAMP Assessment automatically discovers "unknown" external blind spots, such as Shadow IT, stale DNS entries, and exposed infrastructure, and maps them directly to your required federal compliance controls, such as NIST 800-53 and FedRAMP 20x Key Security Indicators (KSIs). By translating these technical vulnerabilities directly into deterministic compliance data, ThreatNG provides the objective, empirical evidence required to fuel your persistent validation pipelines. This empowers you to confidently accelerate your path to an Authority to Operate (ATO), effortlessly generate the machine-readable authorization packages required by 2026, and definitively prove your continuous security posture to 3PAO auditors before an assessment ever begins.
For Service Providers (MSSPs & 3PAOs)
Differentiate your continuous monitoring (ConMon) and advisory services and drive high-margin revenue by offering automated "Persistent Validation as a Service." With our automated mapping to FedRAMP KSIs, you can provide a continuous "Adversary’s View" and an evidentiary record of external boundary due diligence that internal scanners simply cannot capture. This capability enables your federal and enterprise clients to translate complex external threat data into the precise machine-readable evidence and Quarterly Ongoing Authorization Reports required to maintain their federal contracts. As a result, you can effortlessly justify continuous security retainers, eliminate the "Hidden Tax on the SOC" associated with manual evidence collection, and elevate your role from a technical vendor to an indispensable strategic partner in federal compliance.
Frequently Asked Questions: ThreatNG External GRC Assessment & Open FAIR™ Mapping
-
Cyber Risk Quantification (CRQ) is the process of evaluating cybersecurity risks in financial terms rather than relying on subjective "red-yellow-green" heat maps or technical CVSS scores. The Factor Analysis of Information Risk (Open FAIR™) is the internationally recognized standard model for CRQ. Instead of guessing the severity of a threat, the FAIR model provides a methodology to calculate risk by measuring two objective variables: Probable Frequency and Probable Magnitude of Future Loss. ThreatNG's platform leverages this standard by taking technical vulnerabilities, such as a dangling DNS record or an exposed cloud bucket, and mapping its findings directly to the Open FAIR™ framework. By referencing our comprehensive mapping document, organizations can seamlessly integrate these objective external findings into their FAIR calculations to establish mathematically sound financial metrics (in dollars and cents) that the boardroom and regulators can readily understand.
-
Traditional internal compliance audits heavily rely on questionnaires, credentialed scans, and private network access. This structurally blinds them to unmanaged external assets, shadow IT, and employee credentials actively circulating on the dark web. ThreatNG’s External GRC Assessment operates exactly like a sophisticated threat actor, utilizing unauthenticated, continuous discovery to map your organization's digital footprint from the outside in. This provides the critical external ground truth required to validate internal policies and ensure your actual digital presence aligns with corporate governance mandates.
-
The "counterfactual problem" is the economic challenge of proving the financial value of a disastrous data breach that your security team successfully prevented. Because a stopped attack doesn't appear on a balance sheet, CISOs historically struggle to justify security budgets. By automatically mapping external attack surface discoveries to the Open FAIR™ framework and referencing the mapping document, ThreatNG provides the exact empirical data required to fuel your financial risk models. This allows security leaders to accurately calculate their Annualized Loss Exposure (ALE) and definitively prove ROSI by showing the board exactly how much potential financial loss was averted through specific remediation efforts, ultimately optimizing capital allocation.
-
In the current regulatory environment, corporate leadership is facing unprecedented scrutiny. The SEC now requires public companies to disclose material cybersecurity incidents within 4 business days, and regulations such as the new Cybersecurity Act explicitly shift personal and financial liability to management. Relying on guesswork or outdated risk matrices leaves executives legally vulnerable. By deploying ThreatNG’s External GRC Assessment and utilizing our Open FAIR™ mappings, executives establish the foundation for a rigorous, actuarially sound standard of care. This mapped intelligence provides the objective evidence required to demonstrate to regulators and auditors that cyber risks were continuously monitored and prioritized based on structured financial methodologies rather than assumptions.
-
In addition to referencing the Open FAIR™ mapping document, ThreatNG natively maps discovered external vulnerabilities directly to the specific controls required by major global frameworks, including PCI DSS, HIPAA, GDPR, and the NIST Cybersecurity Framework. For example, if ThreatNG's continuous discovery engine identifies a publicly exposed database or an unpatched vulnerability within a cardholder data environment, the platform automatically flags these as specific PCI DSS non-compliance issues (such as Requirement 1.2.1 for firewalls or 6.2 for security patches). This eliminates the grueling manual labor of framework mapping and ensures your organization maintains continuous, audit-ready compliance.