Report and Execute
Architecting Operational Velocity with ThreatNG's AI-Enabled Insights
Making informed security decisions requires more than just a comprehensive view of your organization's digital footprint. In the era of machine-speed threats, a "report" can no longer be a static spreadsheet of disconnected alerts; it must be a catalyst for immediate action.
ThreatNG redefines reporting for AI-Enabled External CTEM. We go beyond traditional vulnerability scanning by synthesizing external attack surface data, digital risks, and security ratings into highly engineered, context-rich intelligence. Whether you are generating a granular technical breakdown, an executive summary, or a DarcPrompt for your Enterprise AI, ThreatNG empowers you to prioritize threats, execute mitigation strategies, and achieve true operational velocity.
The Paradigm Shift: DarcPrompt & The Contextual AI Abstraction Layer
Democratizing Elite Cyber Intelligence for Immediate Execution
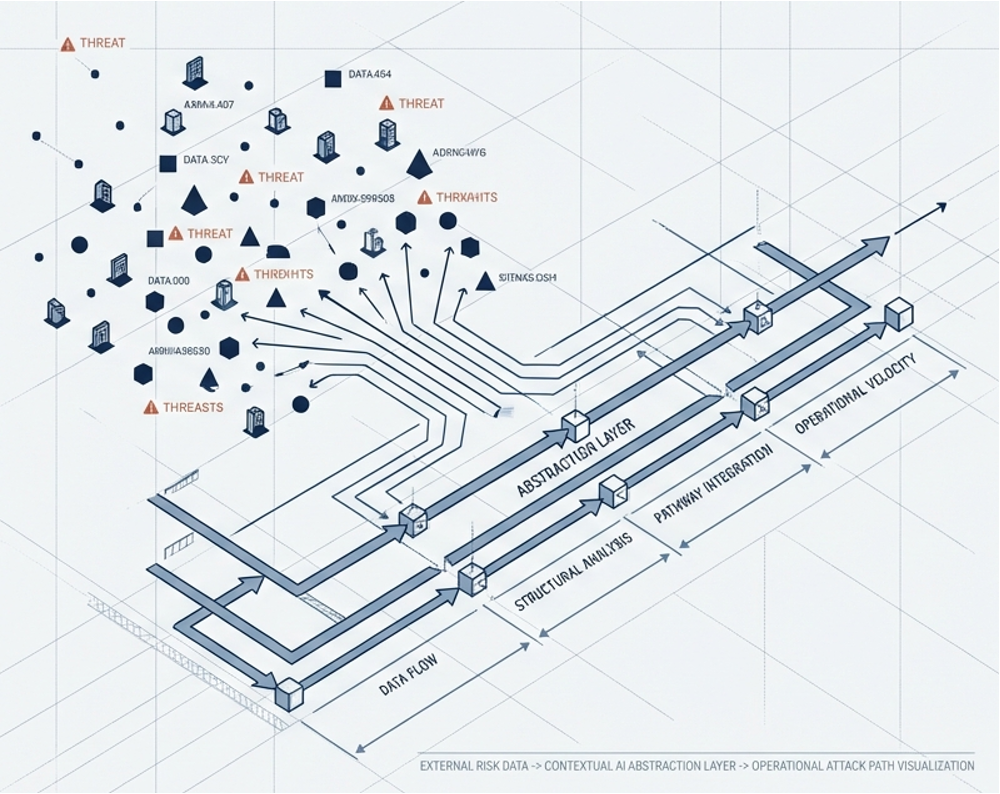
Legacy security tools hand you a "pile of bricks"—noisy data that forces your analysts to become prompt engineers. ThreatNG takes a fundamentally different approach. Our Contextual AI Abstraction Layer automatically synthesizes raw external discovery data and Attack Path Intelligence into a DarcPrompt (Data Assessment and Repeatable Context Prompt).
DarcPrompt is a "Cognitive Exoskeleton" that packages verified ground truth, regulatory context, and optimal instruction sets into a single, highly engineered payload. By copying a DarcPrompt and executing an Air-Gapped Handoff into your own secure Enterprise LLM (such as Microsoft Copilot or ChatGPT Enterprise), your team can safely achieve Bounded Autonomy and undeniable human-verified supervision without ever routing sensitive data through a vendor's API.
The Four Pillars of DarcPrompt Execution
Our DarcPrompt library allows any practitioner, from an L1 analyst to a seasoned CISO, to instantly generate board-ready strategies across four critical pillars:
Pillar I
Core Security Operations & Triage
Instantly generate end-to-end analysis, decompose External Attack Paths, and hunt for Shadow IT and unsanctioned AI exposures.
Pillar II
Strategic Risk & Program Management
Translate technical findings into a sustainable CTEM strategy, align exposures with your contextual Risk Appetite, and interpret X Susceptibility and eXposure Scores.
Pillar III
Governance & Supply Chain
Map technical exposures directly to major compliance frameworks (ISO 27001, NIST, SOC 2) for External GRC Assessments and execute comprehensive Third-Party Risk Management (TPRM) audits.
Pillar IV
Security-Led Growth & Commercialization
Turn security intelligence into revenue by identifying targeted commercial opportunities and mapping monetizable Takedown and Brand Protection strategies.

Unified Reporting for External Attack Surface Management, Digital Risk Protection, and Security Ratings
ThreatNG's digital presence discovery and assessment approach provides a holistic view of an organization's security posture. This comprehensive data is then used to generate various reports empowering organizations to:
Make informed security decisions at all levels (executive and technical).
Prioritize security efforts based on the most critical risks.
Demonstrate a proactive approach to external security for better security ratings.
Gain insights into potential risks beyond traditional security vulnerabilities.
Customize risk assessments based on specific needs and regulations.
Foundational Intelligence Reporting
The Ground Truth That Powers Your Defense
Before AI can act, it needs hallucination-free facts. ThreatNG provides a suite of foundational reports designed to equip both executives and technicians with precise, actionable truth.
Executive-Level Reporting

Security Made Simple: Clear Understanding & Effective Action
ThreatNG executive-level reports are designed for simplicity without sacrificing depth. They comprehensively cover risk levels, offering valuable context through detailed Reasoning and guiding leaders toward effective mitigation strategies through clear Recommendations. Backed by concrete References, these reports empower decision-makers to confidently safeguard digital assets.
Technical Detail Reporting

Precision Through Detail: Equipping Technicians for EASM & DRP
Tailor-made for the security experts investigating the intricate nuances of external risk. These reports provide the granular details required for in-depth investigation, precise remediation, and effective governance, empowering your technical team to tackle digital risks precisely.

Attack Path Intelligence
Translating Technical Risk into Strategic Calm
The engine of our external contextual intelligence is DarChain (Digital Attack Risk Contextual Hyper-Analysis Insights Narrative). DarChain is the sophisticated hyper-analysis engine that powers the External Adversary View. It performs the heavy lifting of multi-stage correlation linking technical vulnerabilities, social exposures, and financial disclosures into a visual, step-by-step exploit chain. By revealing the connective tissue between disparate findings, DarChain identifies the exact Attack Path Choke Points where a single remediation can disrupt dozens of potential adversarial narratives.

Prioritized Reporting


Clear Priorities and Actionable Insights
eXposure Priority Rating Reports simplify the external attack surface by categorizing findings into Critical, High, Medium, Low, and Informational risk severity levels. This ensures everyone grasps immediate priorities, providing swift, structured paths to mitigate digital risks effectively.
Security Ratings Reports


Unveiling Your Digital Landscape
X Susceptibility and eXposure Reports offer immediate, accessible insights into your external risk posture. By measuring both the likelihood of compromise (Susceptibility) and the public visibility of the asset (Exposure), ThreatNG provides an accurate, data-driven benchmark of your digital health.
Inventory Reporting


Concise and Categorized Visibility
eXposure Summary Reports provide a concise, categorized enumeration of all findings, ensuring that decision-makers and technicians alike share a unified understanding of the current attack surface inventory.
Specialized Reports
Unveiling Your Ransomware Exposure
A dynamically generated document that thoroughly examines your vulnerability to ransomware. Using the ThreatNG Breach and Ransomware Susceptibility Score, it evaluates your digital footprint and spotlights specific infection vectors, including Internet-Facing Vulnerabilities, Misconfigurations, Phishing, Precursor Malware Infection, and risks tied to Third Parties.
Uncovering Cybersecurity Posture and Risk Management Practices
A one-stop shop for understanding a company's cyber oversight. It analyzes SEC filings to identify risk disclosures, assess board involvement, pinpoint data privacy risk factors, and evaluate mitigation processes, empowering informed decisions about potential partners and vendors.
The Definitive Outside-In Blueprint for Digital Supply Chain Resilience
A continuous, unauthenticated, outside-in inventory of your entire digital supply chain. Unlike traditional internal SBOMs, the xSBOM maps publicly facing elements such as observable technologies, third-party vendors, shadow SaaS connections, and sensitive code exposures illuminating the blind spots legacy tools cannot reach.

Data Aggregation Reconnaissance Component for Risk Appetite Definition and Representation
Streamline communication and collaboration with ThreatNG's DarcRadar policy management. Customizable risk configurations and scoring models translate complex data into models that align perfectly with your organization's specific Risk Appetite. Dynamic entity definitions ensure your reports encompass everything from brand mentions to third-party vendors, while advanced exception management eliminates noise. DarcRadar ensures your intelligence is focused, relevant, and perfectly scoped for your business reality.
Policy Management
ThreatNG Reporting & DarcPrompt FAQ: Architecting Operational Velocity
-
AI-Enabled External Continuous Threat Exposure Management (CTEM) Reporting is a modern cybersecurity capability that moves beyond static vulnerability scanning. Instead of simply listing exposed assets, ThreatNG synthesizes external attack surface data, digital risks, and security ratings into highly structured, context-rich intelligence. It uses AI not just to filter alerts, but to generate proactive mitigation blueprints, allowing organizations to understand exactly how adversaries might exploit their external blind spots and how to fix them immediately.
-
Legacy External Attack Surface Management (EASM) and Digital Risk Protection (DRP) tools hand security teams a "pile of bricks"—massive, noisy spreadsheets of disconnected alerts that force exhausted analysts to manually correlate data. ThreatNG is fundamentally different because it maps the connective tissue between vulnerabilities using DarChain (Attack Path Intelligence). Instead of a spreadsheet of problems, ThreatNG provides a clear, visual attack path and the exact, board-ready mitigation plan required to break the kill chain.
-
DarcPrompt (Data Assessment and Repeatable Context Prompt) is ThreatNG’s proprietary "Service-as-a-Software" execution tool. It automatically packages verified external ground truth, regulatory context, and highly engineered instruction sets into a single text prompt. Security teams can simply copy and paste this prompt into their own secure Enterprise LLM (like Microsoft Copilot). This eliminates the "Burden of Knowledge," allowing an L1 analyst to instantly generate the strategic output of a senior GRC auditor or offensive threat modeler without needing to be a prompt engineering expert.
-
The "Air-Gapped Handoff" prevents sensitive enterprise vulnerability data from leaking to third-party AI models. Many security vendors bolt reactive chatbots onto their platforms, which secretly route your sensitive attack surface data through external APIs (like OpenAI) to function—a massive compliance red flag. ThreatNG’s Air-Gapped Handoff allows you to take the highly structured DarcPrompt and execute it entirely within your own secured, internally hosted AI environment, ensuring zero API privacy risks and maintaining strict Bounded Autonomy.
-
No. ThreatNG operates entirely outside the firewall with zero internal connectors and zero required permissions. By performing purely unauthenticated, outside-in discovery, the platform avoids the massive deployment friction and "Connector Traps" of legacy ecosystem giants. You gain immediate visibility into shadow IT, unmanaged vendors, and exposed credentials in minutes, not months.
-
ThreatNG directly translates technical external exposures into compliance language. The platform maps external findings directly to major compliance frameworks (such as ISO 27001, NIST CSF, CIS Controls, and SOC 2), highlighting specific control gaps and deficiencies. For TPRM, ThreatNG continuously evaluates the external security posture of your vendors, partners, and supply chain, identifying potential attack paths that run through third parties so you can enforce accountability before a breach occurs.
-
An xSBOM (External Software Bill of Materials) is the definitive outside-in blueprint of an organization's digital supply chain. While traditional SBOMs only catalog internal software components, they completely miss the external perimeter. The ThreatNG xSBOM continuously maps publicly facing elements, observable technologies, third-party vendor integrations, shadow SaaS connections, and sensitive code exposures. It illuminates the blind spots that internal security tools cannot reach.
-
ThreatNG allows Managed Security Service Providers (MSSPs) to scale elite consulting services without increasing headcount. By using the DarcPrompt library, an MSSP account manager can instantly generate highly monetizable, board-ready strategic assessments for their clients. Specialized reporting for Opportunity Finding, Takedown & Brand Protection, and Risk Appetite Assessments allows MSSPs to continuously identify new service gaps, proving ROI and expanding client contracts with 100% predictable, entity-centric budgeting.