External Open FAIR™ Assessment
Stop Guessing, Start Quantifying: Protect Your Legacy and Bottom Line with External GRC Assessment: Open FAIR™ Mapping
The era of defending your enterprise's security posture with subjective, color-coded heat maps is officially over. With the SEC's strict four-day material incident disclosure rules and sweeping new regulations, such as the Cybersecurity Act (NIS2 transposition), that explicitly shift responsibility to management, executives now face unprecedented professional risk and personal financial liability for cyber negligence. You can no longer afford the "crisis of context" where technical vulnerability scores fail to translate into actual business impact. ThreatNG’s External Open FAIR™ Mapping bridges this critical communication gap between the SOC and the boardroom. By automatically translating objective, "outside-in" discoveries into actuarially approved financial metrics, we solve the counterfactual problem in cybersecurity. Discover your true Annualized Loss Exposure (ALE) and transform your Continuous Threat Exposure Management (CTEM) program from a technical guessing game into a legally defensible, financially sound corporate governance strategy.
Defend Your Legacy and Your Bottom Line:
The Boardroom Imperative for Open FAIR™ Mapping

Insulate Leadership from Personal Liability and Regulatory Fines
If an orphaned cloud asset or a compromised credential causes a breach tomorrow, could you prove to federal regulators that your team logically prioritized that risk? Failing to ensure adequate security measures can now result in severe corporate fines of up to 2% of annual turnover, personal financial liability, and even a ban on holding office for corporate directors. Our automated Open FAIR™ mappings abandon subjective guesswork in favor of a mathematically defensible standard of care. By proving you prioritize remediation based on continuous Cyber Risk Quantification (CRQ), you secure your perimeter, protect your Directors & Officers (D&O) coverage, and safeguard your professional legacy against the harshest regulatory scrutiny.
Solve the "Counterfactual Problem" to Prove Security ROI
Board members are deeply frustrated by requests for security budgets that are justified by technical jargon rather than financial reality. ThreatNG empowers you to speak the only language the boardroom understands: dollars and cents. By calculating the probable frequency and probable magnitude of future loss, our platform determines your exact Annualized Loss Exposure (ALE) based on real-world threat intelligence. This allows you to definitively prove your Return on Security Investment (ROSI) by demonstrating the exact monetary value of the breaches you prevent. Stop fighting for budget and start optimizing your capital allocation using economic principles, such as the Gordon-Loeb model, to transition from a technical cost center to a strategic business partner.

Eliminate the "Outside-In" Blind Spot for Continuous Compliance
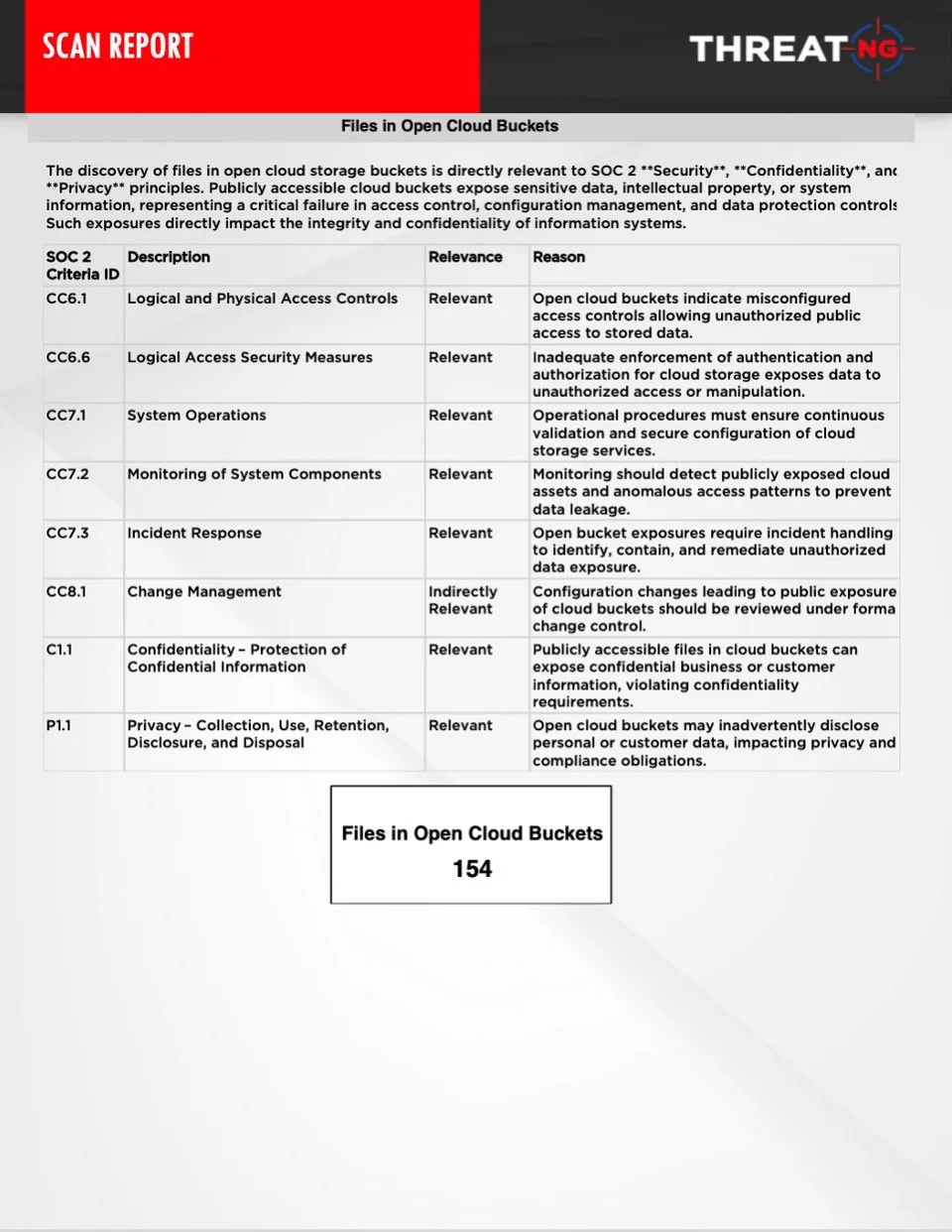
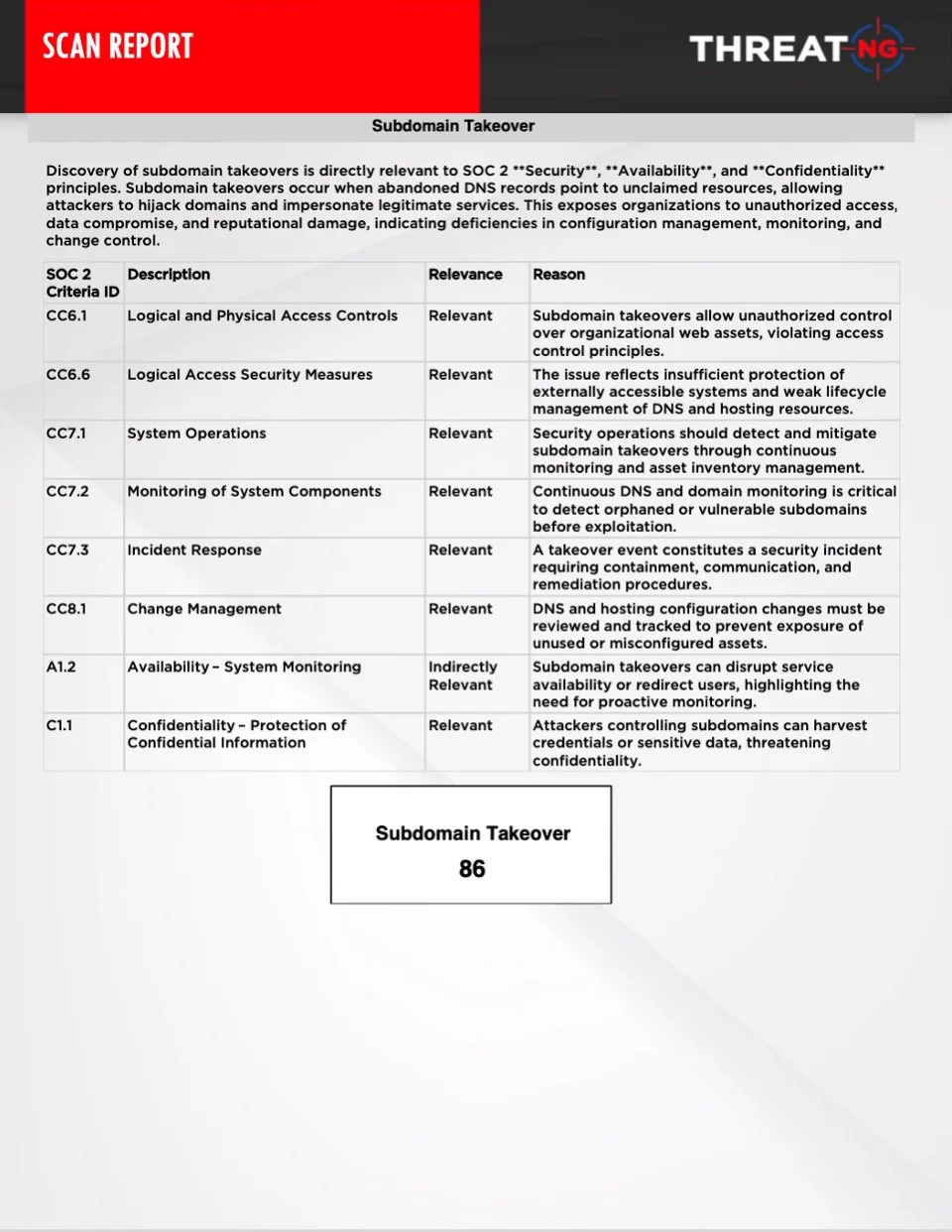
Your team's dedication to building a robust internal GRC program and achieving certifications like SOC 2 is commendable, but internal audits are structurally blind to the outside world. They cannot see the shadow IT spun up by third-party vendors or the executive credentials actively circulating on the dark web. ThreatNG's zero-touch external discovery serves as your ultimate early-warning system, revealing the exact same vulnerabilities a sophisticated threat actor sees. Furthermore, our platform eliminates the grueling manual labor of framework mapping by directly translating discovered external risks into specific non-compliance issues for PCI DSS, HIPAA, GDPR, and the NIST CSF. Validate your internal controls against external reality to ensure your organization is continuously audit-ready.
Boardroom-Ready Attribution Reports: Translating Cyber Exposure into Financial Truth
The reports generated by ThreatNG’s External GRC Assessment capability abandon confusing technical jargon in favor of clear, actuarial financial metrics. By feeding unauthenticated external discovery data directly into the Open FAIR™ framework, these reports transform technical noise into "Legal-Grade Attribution". Alongside mapping external vulnerabilities to specific compliance frameworks such as PCI DSS, GDPR, and NIST CSF, these prioritized reports provide your GRC team with the precise financial context needed to confidently communicate risk to stakeholders, justify remediation budgets, and demonstrate a mathematically defensible standard of care.

Why ThreatNG?
For End Organizations
Replace the anxiety of subjective, point-in-time audits with the absolute certainty of continuous, mathematically defensible assurance. ThreatNG’s External GRC Assessment automatically discovers 'unknown' external blind spots, such as Shadow IT and exposed infrastructure, and maps them directly to your required compliance controls, such as SOC 2, PCI DSS, and GDPR. By mapping these technical vulnerabilities directly to the Open FAIR™ framework via our comprehensive mapping capabilities, ThreatNG provides the objective, empirical data required to fuel your organization's financial risk models. This empowers you to confidently calculate actuarial metrics, definitively prove your Return on Security Investment (ROSI) to the board, and legally insulate your executives from personal liability before a breach ever occurs.
For Service Providers (MSSPs)
Differentiate your vCISO services and drive high-margin revenue by offering "Cyber Risk Quantification as a Service." With our automated Open FAIR™ mapping, you can provide a continuous 'Adversary’s View' of an evidentiary record of external due diligence that internal scanners simply cannot capture. This capability enables your enterprise clients to translate complex threat data into financially understandable metrics (dollars and cents). As a result, you can effortlessly justify security retainers, show tangible return on investment during quarterly reviews, and elevate your role from a technical vendor to a strategic business partner.
Frequently Asked Questions: ThreatNG External GRC Assessment & Open FAIR™ Mapping
-
Cyber Risk Quantification (CRQ) is the process of evaluating cybersecurity risks in financial terms rather than relying on subjective "red-yellow-green" heat maps or technical CVSS scores. The Factor Analysis of Information Risk (Open FAIR™) is the internationally recognized standard model for CRQ. Instead of guessing the severity of a threat, the FAIR model provides a methodology to calculate risk by measuring two objective variables: Probable Frequency and Probable Magnitude of Future Loss. ThreatNG's platform leverages this standard by taking technical vulnerabilities, such as a dangling DNS record or an exposed cloud bucket, and mapping its findings directly to the Open FAIR™ framework. By referencing our comprehensive mapping document, organizations can seamlessly integrate these objective external findings into their FAIR calculations to establish mathematically sound financial metrics (in dollars and cents) that the boardroom and regulators can readily understand.
-
Traditional internal compliance audits heavily rely on questionnaires, credentialed scans, and private network access. This structurally blinds them to unmanaged external assets, shadow IT, and employee credentials actively circulating on the dark web. ThreatNG’s External GRC Assessment operates exactly like a sophisticated threat actor, utilizing unauthenticated, continuous discovery to map your organization's digital footprint from the outside in. This provides the critical external ground truth required to validate internal policies and ensure your actual digital presence aligns with corporate governance mandates.
-
The "counterfactual problem" is the economic challenge of proving the financial value of a disastrous data breach that your security team successfully prevented. Because a stopped attack doesn't appear on a balance sheet, CISOs historically struggle to justify security budgets. By automatically mapping external attack surface discoveries to the Open FAIR™ framework and referencing the mapping document, ThreatNG provides the exact empirical data required to fuel your financial risk models. This allows security leaders to accurately calculate their Annualized Loss Exposure (ALE) and definitively prove ROSI by showing the board exactly how much potential financial loss was averted through specific remediation efforts, ultimately optimizing capital allocation.
-
In the current regulatory environment, corporate leadership is facing unprecedented scrutiny. The SEC now requires public companies to disclose material cybersecurity incidents within 4 business days, and regulations such as the new Cybersecurity Act explicitly shift personal and financial liability to management. Relying on guesswork or outdated risk matrices leaves executives legally vulnerable. By deploying ThreatNG’s External GRC Assessment and utilizing our Open FAIR™ mappings, executives establish the foundation for a rigorous, actuarially sound standard of care. This mapped intelligence provides the objective evidence required to demonstrate to regulators and auditors that cyber risks were continuously monitored and prioritized based on structured financial methodologies rather than assumptions.
-
In addition to referencing the Open FAIR™ mapping document, ThreatNG natively maps discovered external vulnerabilities directly to the specific controls required by major global frameworks, including PCI DSS, HIPAA, GDPR, and the NIST Cybersecurity Framework. For example, if ThreatNG's continuous discovery engine identifies a publicly exposed database or an unpatched vulnerability within a cardholder data environment, the platform automatically flags these as specific PCI DSS non-compliance issues (such as Requirement 1.2.1 for firewalls or 6.2 for security patches). This eliminates the grueling manual labor of framework mapping and ensures your organization maintains continuous, audit-ready compliance.